It’s Not If But When: The EDR Alert That Saved a Company From Total Ransomware Lockdown
The notification came in at 3:47 on a Tuesday afternoon. A single alert from an endpoint detection and response system flagged unusual file encryption activity on three workstations in the accounting department. Within seconds, automated protocols kicked in. The affected machines were isolated from the network. User accounts were suspended. The incident response team was notified.
What could have been a complete business shutdown became a contained event. The company kept operating. Payroll went out on time. Customer data remained private. The only lasting damage was a few hours of lost productivity and a renewed appreciation for proper security monitoring.
This scenario plays out more often than most business owners realize. The difference between a minor security incident and a catastrophic ransomware lockdown often comes down to seconds and the right technology stack. For Los Angeles businesses, where the cost of downtime can reach thousands of dollars per hour, understanding how modern threat detection works isn’t just technical knowledge. It’s business survival.
Why Los Angeles Businesses Are Prime Targets for Ransomware Attacks
California’s economy represents one of the largest in the world. If the state were an independent nation, it would rank among the top five economies globally. This economic concentration creates a target-rich environment for cybercriminals. Los Angeles, as the state’s largest city, hosts everything from entertainment giants and manufacturing facilities to healthcare providers and professional services firms.
Small and medium sized businesses in the LA area face particular risk. These organizations often maintain valuable data but lack the security resources of enterprise corporations. Cybercriminals understand this dynamic perfectly. They know that a regional construction company with fifty employees processes sensitive financial information. They understand that a boutique law firm in Century City holds client communications protected by privilege. They recognize that a medical practice in Encino maintains years of patient health records.
The California Attorney General’s office reported that ransomware attacks against businesses in the state increased substantially in recent years. Attackers have shifted from broad, untargeted campaigns to precise strikes against organizations with the most to lose and the least protection.
“Attackers don’t discriminate by company size anymore. They look for vulnerability and willingness to pay,” explains Juan Turcios, President and CEO of IT Training & Consulting, Inc. “A small accounting firm might have weaker defenses than a large corporation, but their data is just as valuable on the black market.”
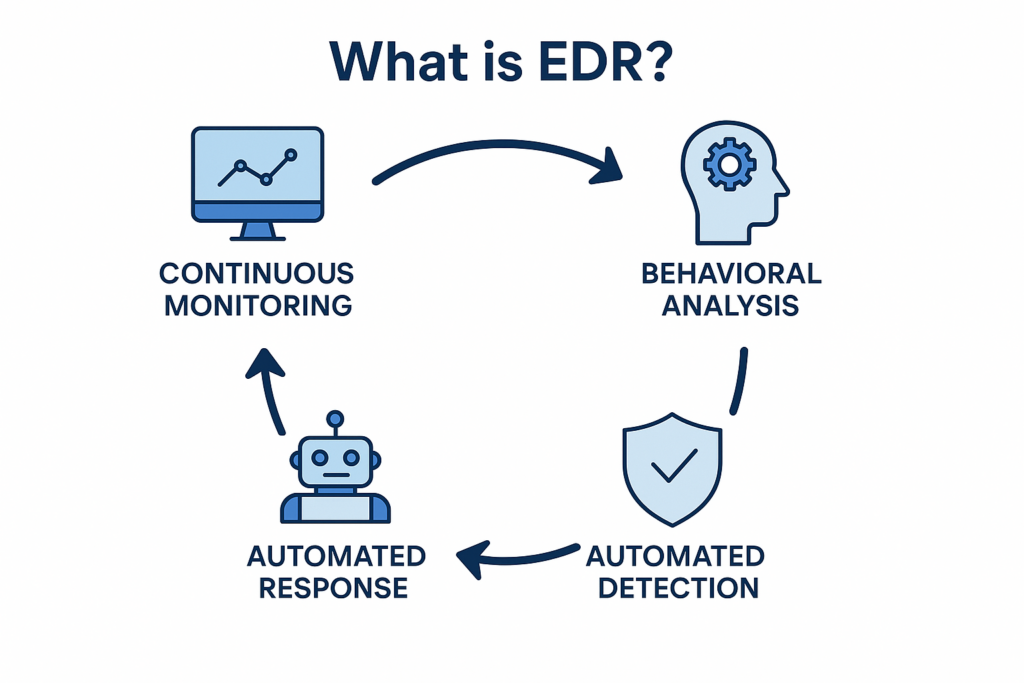
Understanding EDR: More Than Traditional Antivirus
Endpoint detection and response represents a fundamental shift in how organizations protect their devices. Traditional antivirus solutions rely on signature based detection. They maintain databases of known malware samples and compare files against these lists. This approach worked reasonably well when threats were relatively static and new malware emerged slowly.
Modern ransomware operates differently. Attackers constantly modify their code to evade signature based detection. They use polymorphic techniques that change file characteristics while maintaining malicious functionality. They deploy living off the land strategies that leverage legitimate system tools for harmful purposes.
EDR solutions address these challenges through behavioral analysis. Rather than asking whether a file matches known malware signatures, EDR asks whether file behavior appears malicious. Does a process suddenly begin encrypting thousands of files? Is a user account attempting to access systems it has never touched before? Are unusual commands executing across multiple workstations simultaneously?
The technology continuously monitors endpoint activity, collecting telemetry data that security teams can analyze for signs of compromise. When suspicious behavior occurs, EDR tools can respond automatically. They isolate affected devices, terminate malicious processes, and alert human analysts who can investigate further.
The Anatomy of a Contained Ransomware Attack
The company that received the 3:47 alert didn’t know they were under attack until after the threat had been neutralized. Here is what actually happened in those critical moments.
The initial compromise occurred through a phishing email received by a senior accountant. The message appeared to come from a trusted vendor with whom the company had worked for years. It included an invoice that required immediate attention. The accountant opened the attachment, which installed a small payload designed to establish persistence on the system.
For the next several hours, the malware remained dormant. It communicated with command and control servers, downloaded additional components, and mapped the network to identify high value targets. The attackers planned to execute their encryption routine during off hours when detection would be less likely.
Their mistake came during the reconnaissance phase. When the malware attempted to access the domain controller using stolen credentials, the EDR solution flagged the behavior as anomalous. The system recognized that this particular workstation had never previously attempted domain administration functions. It quarantined the device and blocked the authentication attempt.
The attackers pivoted to other compromised machines, but the EDR solution had already escalated its monitoring. When encryption processes launched on three additional workstations, automated responses contained the threat within seconds. Security analysts reviewing the incident later confirmed that the entire attack timeline from initial compromise to containment spanned less than four hours, with actual encryption lasting only thirty seconds before isolation.
Why Traditional Backups Aren’t Enough Anymore
Many business owners believe that regular backups provide sufficient protection against ransomware. This thinking reflects an older threat model where attackers simply encrypted data and demanded payment for decryption keys. Organizations with good backups could restore their systems and ignore the ransom demand.
Modern ransomware operators have adapted. They now exfiltrate data before encryption, threatening to publish sensitive information if victims refuse to pay. A medical practice might face not just operational disruption but public exposure of patient records. A law firm could see privileged client communications posted online. A manufacturing company might have proprietary designs released to competitors.
This double extortion model changes the calculus entirely. Even organizations with perfect backups face significant pressure to pay ransoms. The EDR solution that detected the attack prevented data exfiltration by stopping the encryption process before attackers could complete their data theft.
“Backups remain essential, but they’re no longer sufficient on their own,” says Nestor Turcios, IT Field Technician. “We design security architectures that assume attackers will attempt to breach defenses. The question is whether we can detect and stop them before they accomplish their objectives.”
The Role of Managed Detection and Response
Effective EDR implementation requires more than software installation. Organizations must configure detection rules appropriately, tune alerting thresholds to avoid false positives, and maintain staffing for 24/7 monitoring. Small and medium businesses rarely possess these resources internally.
This reality has driven growth in managed detection and response services, where specialized providers handle security monitoring on behalf of client organizations. These providers maintain security operations centers staffed by analysts who investigate alerts and coordinate responses. They apply threat intelligence gathered across their entire client base, identifying emerging attack patterns before they become widespread.
For Los Angeles businesses, partnering with a local provider offers additional advantages. Regional providers understand California’s regulatory landscape, including privacy requirements under the California Consumer Privacy Act. They maintain relationships with local law enforcement and can assist with incident reporting obligations. They respond to physical security needs when onsite intervention becomes necessary.
Building Defense in Depth
No single security control provides complete protection. Effective security requires layered defenses that compensate for individual control failures. EDR represents one critical layer, but it functions best within a comprehensive security architecture.
Network segmentation limits the damage attackers can cause after compromising a single device. Properly segmented networks isolate sensitive systems from general purpose workstations. A compromised accounting computer cannot easily reach the file server containing HR records. An infected marketing laptop cannot communicate with manufacturing control systems.
Access controls ensure that users maintain only the permissions necessary for their roles. The accountant who opened the phishing email did not require domain administrator privileges. Regular access reviews prevent privilege creep that attackers exploit during lateral movement.
Security awareness training reduces the likelihood of initial compromise. Employees who recognize phishing attempts represent a critical control layer. Training programs that simulate real attacks help organizations identify vulnerable users and provide targeted education.
Patch management closes known vulnerabilities that attackers exploit. The ransomware variant used in this attack leveraged a vulnerability for which patches existed months before the incident. Regular patching would have prevented the initial compromise entirely.
California’s Unique Regulatory Landscape
Businesses operating in California face specific compliance obligations that influence security requirements. The California Consumer Privacy Act imposes strict rules regarding personal information protection. Organizations experiencing data breaches must notify affected individuals and potentially face enforcement actions from the Attorney General.
Healthcare providers must comply with California’s medical privacy laws, which in some cases exceed federal HIPAA requirements. The Confidentiality of Medical Information Act creates additional obligations for organizations handling patient data.
Financial institutions face oversight from the California Department of Financial Protection and Innovation. Recent rulemaking has expanded security requirements for organizations handling consumer financial information.
These regulatory obligations make ransomware prevention particularly important for California businesses. A security incident triggers not just operational disruption but potential legal liability and regulatory penalties. The organization saved by the EDR alert avoided these compounding consequences entirely.
The Economics of Prevention vs. Response
Ransomware costs extend far beyond ransom payments themselves. Organizations experiencing successful attacks face incident response expenses, legal fees, regulatory fines, business interruption losses, and reputational damage that affects future revenue.
The average cost of a ransomware attack against small and medium businesses now exceeds the annual security budgets of most organizations in this category. According to cybersecurity researchers, the average ransom demand increased substantially between 2023 and 2024, with payments frequently reaching six figures.
Downtime costs often exceed ransom demands by significant margins. A manufacturing operation losing production capacity faces immediate revenue losses plus potential penalties for missed customer commitments. A professional services firm losing billable hours confronts direct revenue impacts that compound over time.
The organization protected by the EDR alert avoided these costs entirely. Their investment in security monitoring represented a fraction of what even a single day of downtime would have cost. This economic reality drives adoption of managed security services among businesses that previously viewed security as an unnecessary expense.
What Every Business Leader Should Ask Their IT Provider
Business owners and executives should understand their organization’s security posture regardless of who manages their technology. The following questions help evaluate whether current protections match evolving threats:
How do you detect threats that bypass traditional antivirus? Understanding whether your provider relies solely on signature based detection or employs behavioral monitoring reveals significant differences in protection levels.
What is our incident response process? Organizations should have documented procedures for security events, including communication plans, escalation paths, and recovery steps. These procedures should be tested regularly through exercises that validate their effectiveness.
How quickly can we isolate compromised devices? Response time measurements provide concrete metrics for security effectiveness. Organizations should understand the gap between detection and containment.
Who monitors our systems outside business hours? Attacks frequently occur during evenings and weekends when staffing levels are lowest. Understanding after hours coverage reveals whether threats will be detected promptly.
What threats have you blocked recently? Regular security reporting should include information about prevented attacks. This data demonstrates the value of security investments and helps organizations understand threat landscapes.
The Human Element in Security Operations
Technology alone cannot stop sophisticated attacks. The EDR alert that saved the company required human analysts to investigate, validate, and coordinate response activities. These analysts brought contextual understanding that automated systems cannot replicate.
They recognized that the encryption activity occurred during normal business hours, which contradicted typical ransomware behavior patterns. This observation suggested the attackers had either miscalculated or faced technical constraints that forced earlier execution. The analysts used this insight to search for additional compromised systems that might have triggered the encryption prematurely.
They communicated effectively with business leadership during the incident. Technical security events create anxiety among executives concerned about business impacts. Skilled analysts translate technical details into business implications, helping leadership make informed decisions under pressure.
Preparing for the Inevitable
The cybersecurity community frequently states that organizations face not a question of whether they will experience attacks but when. This framing acknowledges the reality that determined attackers will eventually find ways past perimeter defenses. The goal shifts from perfect prevention to rapid detection and effective response.
Organizations that accept this reality invest differently than those seeking impregnable defenses. They maintain detection capabilities that identify intrusions quickly. They develop response capabilities that contain threats effectively. They test these capabilities regularly through exercises that reveal weaknesses before real attackers exploit them.
They also maintain relationships with security providers who can supplement internal capabilities during incidents. Even organizations with strong internal security teams benefit from external perspectives and additional resources during major events. These partnerships often determine whether incidents become minor interruptions or business threatening crises.
The company saved by the EDR alert had invested in this approach. They accepted that prevention would never be perfect. They built detection and response capabilities that assumed compromise. When attackers inevitably targeted them, these investments paid their full return in thirty seconds of automated response.
A Local Perspective on Regional Threats
Los Angeles businesses face threat patterns that reflect the region’s economic diversity. Entertainment companies contend with attackers seeking unreleased content and intellectual property. Healthcare organizations confront threats from criminal groups targeting patient data. Manufacturing facilities face industrial espionage and operational disruption risks.
These varied threats require tailored defenses rather than generic security approaches. A law firm requires different protections than a logistics company. A retail operation faces different risks than a professional services provider. Security architectures must account for these differences while maintaining consistent protection levels across the organization.
Local security providers understand these nuances in ways that national firms with remote delivery models cannot match. They see threat patterns emerging across their client base. They develop relationships with regional law enforcement and industry groups. They respond physically when situations require onsite presence.
The Future of Ransomware Defense
Ransomware attackers continue evolving their techniques in response to improved defenses. Recent developments include ransomware as a service models that lower barriers to entry for would be attackers. Affiliates can now license ransomware platforms from developers, sharing proceeds from successful attacks while developers handle technical maintenance.
Attackers increasingly target managed service providers themselves, seeking to compromise multiple clients through a single breach. These supply chain attacks exploit trust relationships between service providers and their customers. Defenses must account for risks introduced through vendor access.
Artificial intelligence offers both new threats and new defenses. Attackers use AI to craft more convincing phishing messages and automate reconnaissance activities. Defenders use AI to analyze behavioral patterns at scales impossible for human analysts. This arms race will continue driving innovation on both sides.
Taking Action Before the Alert
The organization protected by the EDR alert did not know they would face a ransomware attack on that Tuesday afternoon. They had invested in security without knowing when or whether that investment would prove valuable. They maintained detection capabilities without certainty that threats would materialize.
This uncertainty characterizes security investments generally. Organizations cannot predict attack timing or verify that protections will work until tested. They must maintain defenses continuously despite never knowing whether current efforts are preventing attacks that would otherwise occur.
Yet the alternative remains unacceptable. Organizations that neglect security face predictable consequences when attackers eventually target them. The question is not whether attacks will happen but whether organizations will survive them.
For Los Angeles businesses, the choice is clear. Invest in detection and response capabilities before the alert arrives. Build relationships with security providers who can respond when seconds count. Accept that attacks will come and prepare accordingly.
Your Next Step Toward Real Protection
The difference between a contained incident and a business ending disaster often comes down to preparation. Organizations that invest in modern threat detection maintain capabilities that stop attacks before encryption completes. They avoid the downtime, costs, and reputational damage that follow successful ransomware.
IT Training & Consulting, Inc. helps Los Angeles businesses build these capabilities through managed security services that include EDR deployment and 24/7 monitoring. Our team understands local threat patterns and regulatory requirements. We respond quickly when alerts trigger and work continuously to improve client security postures.
Don’t wait for an alert to discover whether your organization can survive an attack. Contact us today at (844) 804-4882 or reach out through our contact page to discuss how we can help protect your business from ransomware and other modern threats.